Frequently Asked Questions
How can Grassroots IT ensure the security of our mobile devices?
Our Mobile Device Management solutions prioritise security at all times. We implement measures like encryption, remote wipe capabilities, and regular security patches to protect company data and user privacy.
Is it possible to scale up or down your services based on changes within our business?
Certainly, our End-User Computing services are scalable. We understand that your business priorities and goals can change over time Whether your business is expanding, contracting, or just evolving, we can adapt our services to fit your current and future needs.
What is included in Grassroots IT’s End-User Computing services?
Services cover device management, mobile access, IT procurement, and enhanced security for streamlined business operations.
Can Grassroots IT assist with IT device selection?
Yes, they provide guidance on choosing suitable IT tools tailored to business needs.
Does Grassroots IT provide support for remote work setups?
Yes, Grassroots IT enables seamless and secure remote access, supporting remote work needs with optimised solutions.

Common Cloud Migration Pitfalls (And How to Avoid Them)

Why Change Control Matters (And How It Protects Your Business)

Microsoft 365 Security Features for ISO 27001 Compliance

Maximising Your Microsoft 365 Business Premium Investment: Security Features You Should Be Using

Grassroots IT Achieves Triple ISO Certification

How Conditional Access Policies Can Dramatically Improve Your Cybersecurity Posture

How Microsoft 365 Can Help You Meet Data Protection Regulations in Australia

DLP for Remote Work: Securing Your Data When Your Team Is Everywhere

Stop wasting money on Microsoft 365 licences: why licence management matters

Azure Virtual Desktop for Offshore Teams: Enhancing Remote Work Security

Azure Virtual Desktop for Graphics-Intensive Applications: When to Consider GPU-Enabled Instances

What is Microsoft Intune? A Straightforward Guide

User & Device Lifecycle Management with Entra ID and Intune

Securing Your Remote Workforce with Entra ID and Intune

Driving Inclusive Technology Adoption for Non-profits

How AI and RPA Can Transform Non-Profit Operations

5 Microsoft 365 Tools to Revolutionise your Non-Profit’s Workflow

Navigating the Transition to Windows 11

Developing an IT Hardware Refresh Strategy

Leveraging Technology to Improve the Customer Experience

The Hidden Costs of Aging Technology Infrastructure
The Importance of having a Technology Roadmap for your Business

The top 6 cybersecurity threats to your business and how to prevent them

Microsoft 365 Nonprofit Pricing Plans Explained

The vital role of Managed Detection and Response in a complete Cybersecurity Strategy

Understanding the different Microsoft 365 pricing plans

Cost-effective Cybersecurity Strategies for Non-profits

Getting your business ready for Microsoft Copilot
Common IT Investment Mistakes to Avoid

3 Short Automation Case Studies to Inspire Your Thinking

Three Crucial Elements for your IT Strategy in 2024

The Benefits of Automating Business Processes (and how to spot opportunities)

Microsoft Office 365 Backup: Necessity or waste of money?

Smart Up Your Business: Getting started with AI to streamline business processes

Microsoft Secure Score: Quick Wins for Stronger Cybersecurity

Recognising The Red Flags: 5 Signs Your Business Needs a New Managed Service Provider

How to mitigate the cybersecurity risks of working from home

Decoding Cybersecurity: Busting 10 Common Myths
Boost Your Microsoft 365 Security: 5 Critical Questions to Ask

Building a culture of cybersecurity awareness in your business

3 IT Support metrics that actually matter and why

3 technology trends to watch in 2023
Cybersecurity Policy Resources

Automate repetitive and time-consuming tasks with Power Automate

5 Yammer tips to improve office communication

Voice-to-text dictation with Windows and Office 365

Cheapest and Easiest Way to Manage Email Signatures
How Easy Is It to Guess Your Password?

How to install Office 365 desktop applications on your computer

Office Lens: a OneNote Scanner for your Pocket

Before you panic, here’s how to recall an email in Outlook
Using Conversation Clean Up to Achieve Inbox Zero

How to update your profile picture in Office 365


5 ways the right IT partner can support your in-house IT staff

5 questions board members need to ask about cybersecurity
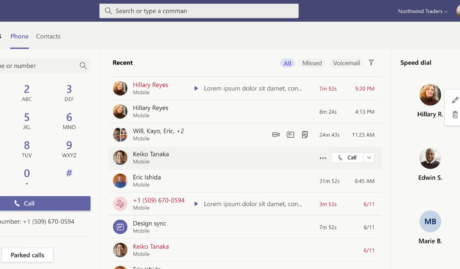
Everything you need to know about Microsoft Teams Phone (aka Teams Calling)
4 Cybersecurity Essentials Every Business Should Have

5 Reasons to Use Microsoft Teams Instead of Emails

What is the Microsoft Power Platform

Choosing the best Managed IT service provider in Brisbane

How to leverage the power of Microsoft 365 app integration

Managed IT Support pricing – everything you need to know (2024)

The top 5 benefits of outsourced IT support

How to get the best from your IT support team

How investing in the right IT services can save your business money

How to run a daily huddle using Microsoft Teams

Office 365 is now Microsoft 365

How Microsoft Teams Enables Seamless Collaboration

Why We Fell In Love with Microsoft Teams While Working from Home

5 Tips for Successfully Outsourcing IT Support

What is the Essential Eight cybersecurity framework
Microsoft Office 365 security tips to implement today

Why an Intelligent Firewall is Critical For Your Network Security

How to identify a phishing email
Office 365 vs. Microsoft 365: What’s the Difference?
How Your Data Can Be Lost in the Cloud (and How to Prevent It)
3 reasons you need to enable Multi-factor Authentication (MFA) today

Why aligning your IT strategy with business goals is critical for success

The Notifiable Data Breach scheme. Is your business ready?

What is a Managed Service Provider and when do I need one?

How we operate remotely between Brisbane, Auckland and Clark

Why do Australian businesses require cyber security? Here are some eye opening stats.
What is your strategy? Do you really have one?
Looking For Help With End-User Computing?
Reach out to our dedicated team today.


